Secure Success: Software & Document Access at Ripcord
This is the third and final article of our security series where we examine the extra layers of security that Ripcord provides each document handled on-site at our facility in Hayward, California.
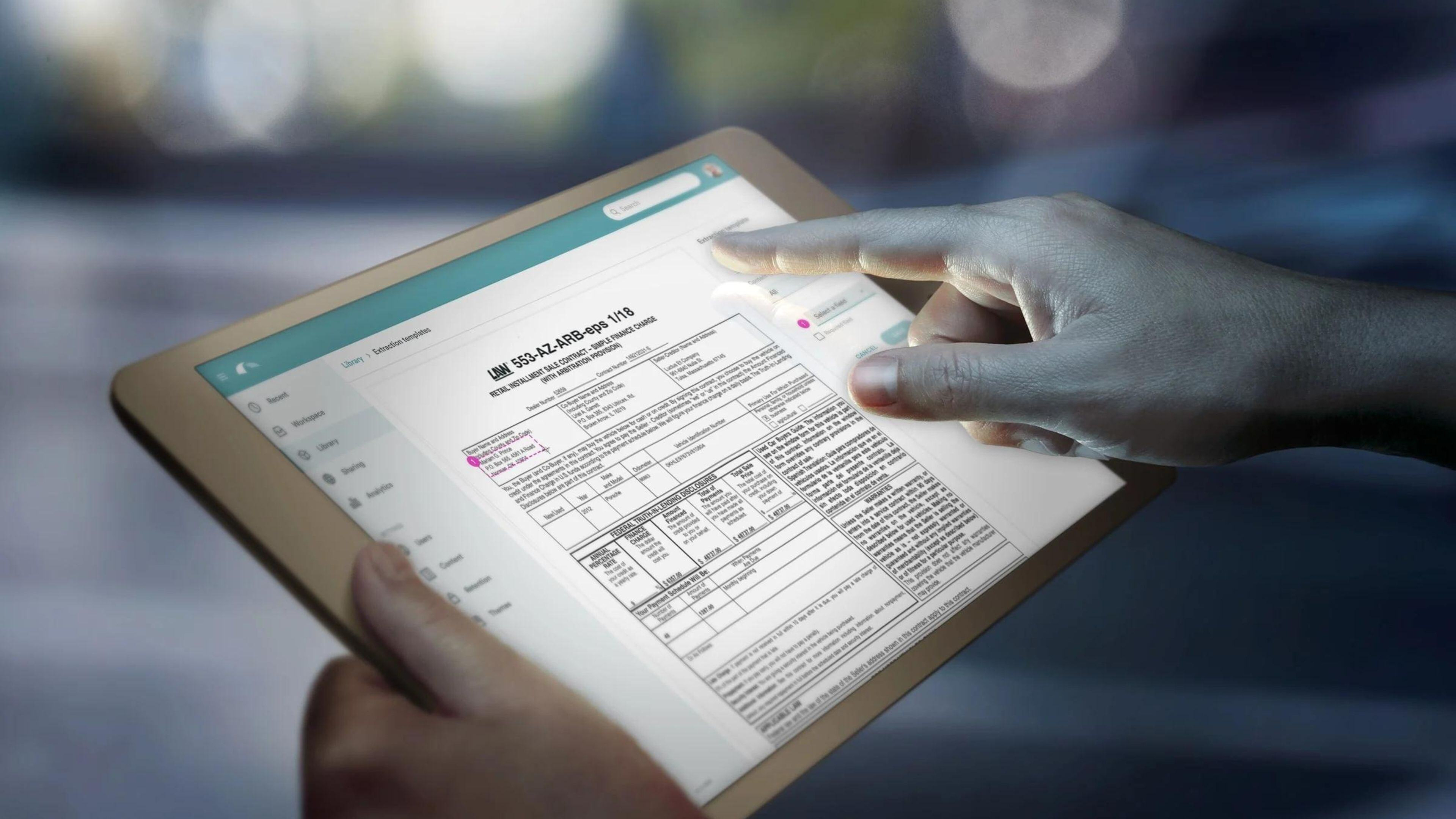
As the world strives to go paperless, businesses are choosing to store the majority of their documents and sensitive information on computers, instead of in back-room boxes. Digitization is the preferred route for converting paper records, as it lessens the chance of loss of high-priority information.
The magnitude and complexity of those documents typically require an extensive software system to secure their safety — be it from any naturally occurring incident or an invasive privacy breach from someone trying to illegally get their hands on a company’s information.
A benefit of the digitization process at Ripcord is that documents are protected at every step of the process, from their journey to our facility to being uploaded to our content management system, Canopy. Today, Ripcord's Chief Product & Technology Officer, Ahson Ahmad, explains the software security measures taken.
Software Security at Ripcord
“We provide end-to-end security of all content that gets in the Canopy; all of the in transit communications are using the Transport Layer Security (TLS) 1.2 protocol, and then once the content rests in Canopy, it’s also being encrypted with AES-256 encryption — and that covers the encryption pieces of how content is structured once it gets into the cloud.”
From Canopy, clients can then choose to manage and share their content directly through the platform or connect it to other applications such as AWS, Oracle, Salesforce, or something of the like. Ahmad says this is because Canopy implements SAML 2.0, an industry standard way to provide authentication that allows Ripcord to integrate with third party identity providers (IDPs).
“A customer may have Active Directory, or Okta, or something else, whether it’s an on-prem solution or a cloud solution," shared Ahmad. "And what we can do with SAML 2.0 is redirect Canopy to the customer’s authentication scheme, and that way the customer can manage their own sets of users, and who has access to the software, entirely on their own, using their own tools.”
Ahmad continues by detailing how the cloud access between different customers is structured. Multitenancy, a software architecture in which a single instance of software runs on a server and is “shared” by multiple groups of users, is something that Ripcord handles in a way that puts their customers at ease, he explains.
“Customers are often concerned about multitenancy, and what it means – ‘Can another customer possibly get access to my data?’ One thing that we do is isolate customer’s data into completely different databases, so even though the user interface (UI) of the software is multitenant, the data is actually single tenant, so there’s no way for a customer to accidentally access content they shouldn’t have access to.”
Extra security protocols are in place to further protect clients’ data once they’re being managed in Canopy. Ahmad says role-based access control (RBAC) is used to restrict system access to unauthorized users, meaning users can only ever see content they are granted access to by a content admin or owner.
“In addition, content that is shared always has 2-factor authentication on it, and a password expiry date, so it’s one variable in implementing data loss prevention (DLP). Then to access the encrypted content we can use AWS Key Management Service (KMS), which is certified under multiple compliance schemes, and we can also use a hardware security module (HSM) for the encryption, which supports the FIPS-140-2 standard, which is one of the more secure standards out there, and that’s used to generate and protect keys related to the encrypted content.”
The software security measures taken at Ripcord are designed to maintain the utmost safety of the documents and data submitted for digitization. Ahmad speaks highly of the protocols in place, especially for the protection it provides customers.
“We take this pretty seriously, because this is sensitive customer data," said Ahmad. "There’s Personally Identifiable Information (PII) data that is involved in our customer’s content and so we’re pretty thorough when it comes to all the different aspects, from the physical layers all the way up to the software layers and processes that extend to it, to make sure that our customer’s content stays secure.”
Ready for more? Head over to the Ripcord YouTube channel to listen to the full interview with Ahson.
/Ripcord%20Logo%20-%20Color%2011.png?width=2000&height=620&name=Ripcord%20Logo%20-%20Color%2011.png)

